The Origins of Cyberspace
Spoiler Alert: The below text goes into detail on William Gibson’s short story “Burning Chrome.”
Cyberspace As 1960s Art and Architecture
The word cyberspace started out as something quite different from what we know it as today. Atelier Cyberspace was created in the 1960s by Danish artist Susanne Ussing and her partner architect Carsten Hoff. Here’s what Hoff said about it in 2015:
To us, "cyberspace" was simply about managing spaces. There was nothing esoteric about it. Nothing digital, either. It was just a tool. The space was concrete, physical.

A famous piece by Susanne Ussing.
Cyberspace In Gibson’s “Burning Chrome”
Cyberspace was first used in fiction by William Gibson in his short story “Burning Chrome.” It’s a 23-page cyberpunk story set in Gibson’s Sprawl world. Before he published it in 1982, he read the story at a science fiction convention. The audience? Four people.
Gibson wasn’t shooting for the stars back then:
All I knew about the word "cyberspace" when I coined it, was that it seemed like an effective buzzword. It seemed evocative and essentially meaningless. It was suggestive of something, but had no real semantic meaning, even for me, as I saw it emerge on the page.
But cyberspace sure found a life well beyond buzz. Let’s look at what cyberspace looked like in “Burning Chrome.”
The Hackers and the Goal
The story features two vigilantes – hardware hacker Automatic Jack and software hacker Bobby Quine. Jack has a cyborg arm after losing one of his real arms in an accident and can connect computers into his stump. Bobby is a womanizer who wants to get rich.
“Chrome” launders money for organized crime and runs a brothel where women can submit their bodies to customers while mentally checking out. Jack and Bobby set out to steal Chrome’s money in cyberspace but she’ll come after them if they don’t cyber-kill (burn) her too. They count on her being physically killed by the mob after losing the all the money.
Thoughts
The real world hacker scene has a lot of freelancers and vigilante types. Sadly, its fair share of misogyny too. Jack and Bobby feel authentic in that sense.
The premise is an interesting bridge between the real criminal world and cybercrime. Burning someone in Gibson’s cyberspace is about fully compromising their computer system and wiping it clean. In today’s real cyberspace, legitimate businesses can have cyber insurance as a path to recovery. But for a criminal organization on the internet, a full compromise may indeed be the end of it all.
If you go all the way to cryptocurrency, you could see even legitimate businesses being killed purely online. The modern adage is “Your keys, your Bitcoin. Not your keys, not your Bitcoin.”
The Hack Itself – Virus vs Ice
In Burning Chrome, attack tools in cyberspace are referred to as viruses. Cyber defense is called ice, or Intrusion Countermeasures Electronics. Viruses can be traded and combined in attacks. Virtual subpoenas and warrants can be used to disguise viruses, i.e. lawful intrusion as cover.
Jack has gotten his hands on a Russian military virus so capable that they have to hold it back. They ride in like cyber cowboys and tear down initial defenses before they reach Chrome’s heart. The heart is defended by black ice – ice that kills – only defeatable by the Russian virus. Here’s a segment from the climax, inside cyberspace:
“Burn the bitch down. I can’t hold the thing back –“
The Russian program, rising through towers of data, blotting out the playroom colors. And I plug Bobby’s homemade command package into the center of Chrome’s cold heart. The squirt transmission cuts in, a pulse of condensed information that shoots straight up, past the thickening tower of darkness, the Russian program, while Bobby struggles to control that crucial second. An unformed arm of shadow twitches from the towering dark, too late.
We’ve done it.
Thoughts
I started thinking Gibson may have invented the term computer virus too. After all, he wrote this short story in the beginning of the 1980s. But it turns out John Von Neumann is considered the originator of self-reproducing computer programs. He began the work in 1949, later published as the "Theory of self-reproducing automata." Automata theory was one of my favorite subjects at university so this piece of history makes me happy.
I would compare Gibson’s viruses to what we today call exploit chains. An exploit of a single bug seldom compromises a whole system these days because modern defenses are deployed in layers. Hence, an attacker needs security bugs in chains to ultimately achieve a full takeover.
Ice is active defense sounding like intrusion detection, segmentation, and diversion. Defending a system on the internet is not just about detecting malicious behavior but also buying time. You lure attackers to systems called honeypots, deliberately set up to be hackable. Or you can set up security canaries that sound an alarm when they're "killed."
Russian military virus sounds to what we refer to as state-sponsored hacking, part of cyberwarfare. Eerily close to the reality we live in.
Gibson's vivid description of cyberspace as a space is a beautiful way of depicting hacks and an alternative to hard hacker fiction. He even uses the term matrix, e.g. Beyond them, the matrix’s illusion of infinite space.
The Literal Use of “Cyberspace”
Burning Chrome does indeed introduce the term cyberspace. Here’s the legendary excerpt:
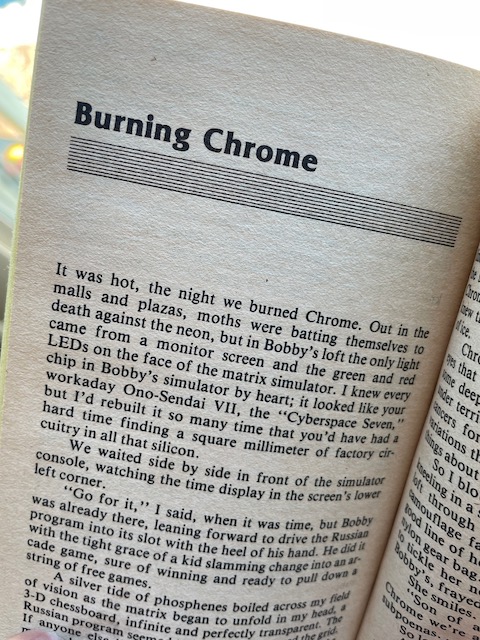
I knew every chip in Bobby’s simulator by heart; it looked like your workaday Ono-Sendai VII, the “Cyberspace Seven,” but I’d rebuilt it so many time that you’d have had a hard time finding a square millimeter of factory circuitry in all that silicon.
The first singular “time” is probably a typo.
Many real world hackers scoff at anything “cyber,” be it cyberwar, cyber defense, or cyberspace. I used to be one of those but have grown to like cyber. It’s a word that immediately invokes the right framing. Cyberspace also identifies the virtual world as a distinct expanse, alongside land, sea, sky, and space.
Cyberspace Today
Cyberspace as a domain for humans really took off with the seminal Declaration of the Independence of Cyberspace by John Perry Barlow. He delivered it 1996 during World Economic Forum in Davos and its leading paragraph does not fall short on gravitas:
Governments of the Industrial World, you weary giants of flesh and steel, I come from Cyberspace, the new home of Mind. On behalf of the future, I ask you of the past to leave us alone. You are not welcome among us. You have no sovereignty where we gather.
25 years later and the possibility of a Splinternet where countries claim network sovereignty is very real. The potential for hacker fiction based on that conflict has not escaped me.
This text was originally published in the October 2021 issue of the Hacker Chronicles newsletter. Subscribe below!
Get the Monthly Newsletter
Subscribe to the Hacker Chronicles newsletter and don’t miss out on movie reviews, hacker insights, publishing updates, and research for upcoming books.
Hitting subscribe will take you to the Buttondown service provider which hosts the newsletter. You can also go to subscribe.hackerfiction.email.